Like it or not, the pandemic year of 2020 saw a record-breaking increase in data breaches and cybersecurity attacks around the world. In fact, a study found that around 78% of employees were not confident of their security companies’ standards, which led to a 91% increase in security budgets for 2021.
The advancement in technology has helped both enterprises and hackers. Companies that invested in the latest cybersecurity systems are doing well, while hackers use the same technology to attack organizations without proper security standards.
If you want comprehensive security compliance software that can be scaled to suit your business needs, look no further than Hyperproof.
Overview of Hyperproof
Compliance protocols and audits have always been complicated. Hyperproof provides SMEs and large enterprises with software to manage their security compliance regulations, collaborate with stakeholders within and outside the business. Hyperproof’s software helps security and compliance teams gain the visibility, efficiency and consistency needed to stay on top of all of their security assurance and compliance work.
Hyperproof’s mission is to create software that allows organizations to demonstrate their strong values and deep commitment to building trust within their community.
What Does Hyperproof Do?
Hyperproof optimizes compliance and security management practices in the enterprise.
→ Compliance Templates
SOC 2, ISO, NIST Privacy, SOX, and many other templates are readily available with Hyperproof. It’s easy to upload the existing framework details to the template and compare them with the requirements.
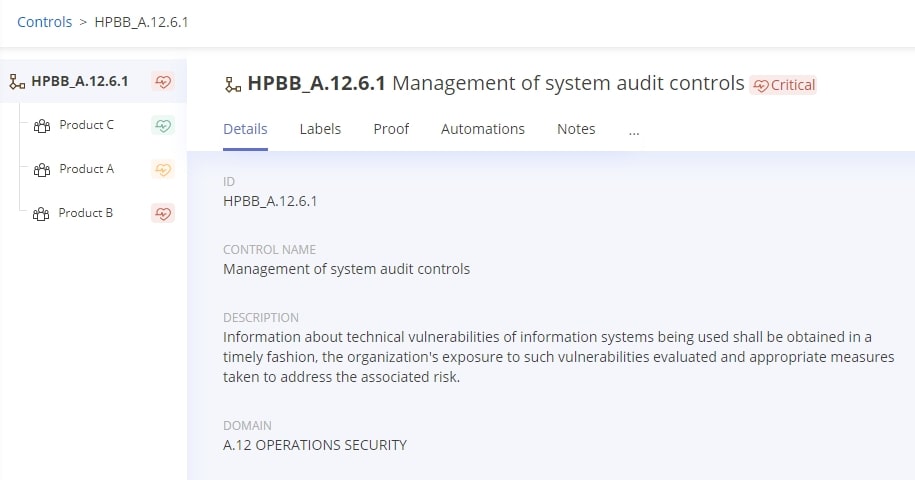
→ Implement common controls to reduce duplicative work
Hyperproof makes it much easier for a user to create one smaller set of security controls and map those controls to various compliance frameworks and legal requirements; this helps organizations efficiently comply with multiple security certifications, standards and regulations.
→ Future Forecasting
Releasing a new product or entering a different market means you also need to look at the new security compliance requirements and adopt them in the enterprise. However, many compliance frameworks have overlapping requirements. Hyperproof makes it possible for you to forecast how much work you need to do to adhere to a new regulation, based on work you’ve already done to meet existing regulations.
→ Streamline and Automate Workflow
Providing security assurance to customers and stakeholders can increase workload and pressure on the employees. The software automates the processes such as notifying people to complete tasks, manually reviewing evidence of controls’ effectiveness, uploading documents, etc. to save time for employees and help create transparency in control performance.
→ Hyperproof and Evidence
Set Standards for Evidence Collection
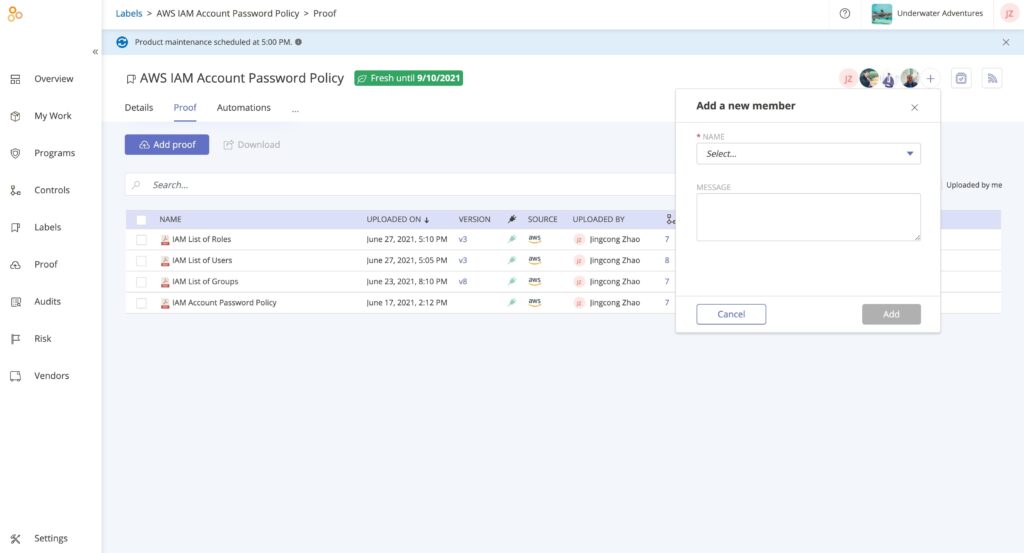
What’s good evidence and what’s not? Compliance professionals can use the software to provide stakeholders details on what evidence they’re looking for and set due dates and automatic notifications to remind people to submit evidence on time.
→ Automate Evidence Collection
Hypersync helps you collect proof from several cloud platforms on a continuous basisas and when you need it. The collected proof comes with the source name, timestamp, and other identifying information to ensure the credibility of the evidence.
→ Re-Use Evidence
A compliance professional can create “labels” or smart folders in Hyperproof and set up automated evidence pulls — so that certain evidence automatically gets stored in specific folders.
A user can link a label to multiple controls — so they can minimize the amount of time spent on collecting evidence.
→ Assess and Minimize Vendor Risks
Hyperproof provides a single home for all vendor information. Enterprises can assess their vendors via security questionnaires; manage remediation tasks; and map vendor information to controls and regulatory frameworks to quickly address your compliance requirements.
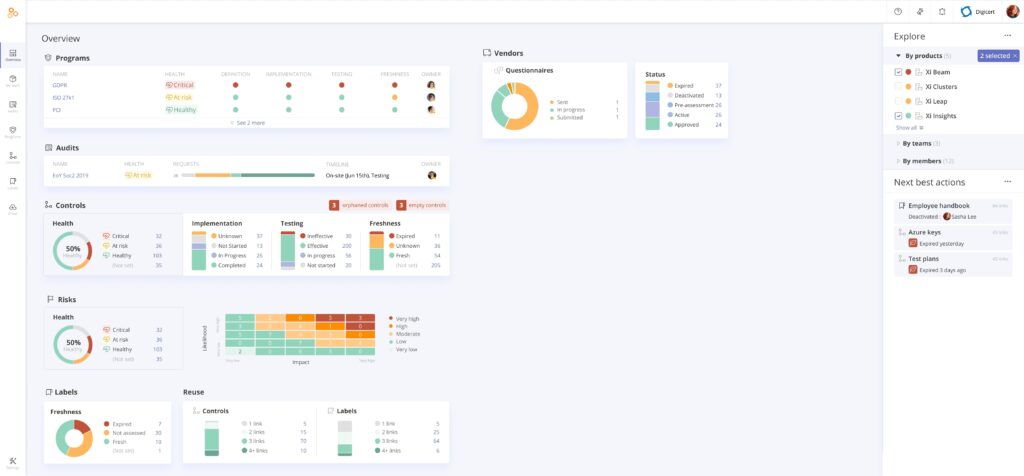
→ Hyperproof’s High-Level Dashboard
Track and Measure Progress
The filters in the dashboard allow you to track and measure the frameworks, gauge compliance standards, and stay up to date.
Program and Audit-Level Reporting

Detailed reports can be generated with just a few clicks. The reports can be directly used during security auditing, thanks to the real-time updates provided by the software.
Hyperproof and System Integrations
Software is useful when it can be integrated with other systems and software applications used in the enterprise. Hyperproof works with a multitude of applications and platforms so that people bring in precisely defined data from various systems as evidence and collaborate with others via software they already use.
Hyperproof integrates with DevOpstorage, security, communication, project, device management and business applications such as GitHub, GitLab, Asana, Jira, Slack, Microsoft Teams, Azure, AWS, GitHub, Cloudflare, Salesforce, Tenable, Sharepoint, Dropbox, and many more. Additionally, Hyperproof can be custom integrated into any application developed by the enterprise using Zapier.

Pricing
The company offers 30 days of free on-boarding and four price packages to suit companies of different sizes.
- Essentials: $4800/year; designed for small businesses; allows up to three users and 2 GB storage space
- Professional: $9600/year; designed for small to medium businesses; unlimited users and 4 GB storage space
- Business: $19,200/year; designed for medium to large businesses; unlimited users, up to 5 allotted teams, and 8 GB storage space
- Enterprise: custom pricing; designed for large and ultra-complex businesses; unlimited users, up to 20 allotted teams, and 16 GB storage space
Final Conclusion
Hyperproof is a complete solution to optimize, automate, and streamline the processes, tasks, security, and compliance teams must complete in order to provide security assurance to customers and meet legal requirements around data protection and security. The scalability of the software makes it a great choice for businesses, irrespective of their size and volume.
Safeguarding the enterprise from cyberattacks according to governmental and industry-wide protocols makes the business more secure and provides opportunities to win high-level project bids.




