Data security is an unavoidable parameter in the corporate world. People invariably prefer to have their data secured at all times and places.
Beyond addressing network and private security threats, you must also safeguard against the loss of data when the laptop or pen drive gets stolen. Wondering how you can do that? Encrypting your hard drive is the key!
Encrypting your hard drive safeguards you against the loss of data even if you lose your laptop. Similarly, if anyone uses your computer/laptop, he won’t be able to access your data because it is encrypted.
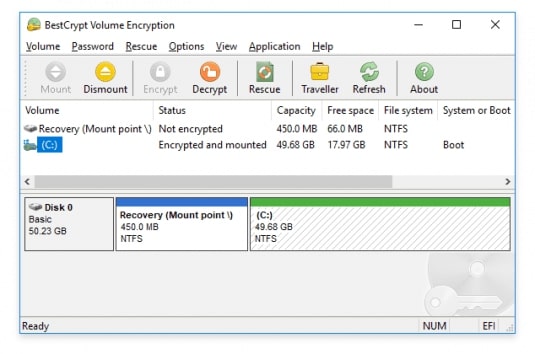
If you are looking for the best hard disc encryption software to enjoy the peace of mind, Jetico’s BestCrypt Volume Encryption is your best bet!

Let us dive deep into how this is the best way to safeguard all the data stored in your removable or fixed devices.
Jetico’s BestCrypt Volume Encryption Delivers Rich Returns For Your Organization
One of the top advantages that come with the use of BestCrypt Volume Encryption is that it encrypts the entire data on hard drives and prevents it from leaking. Since the encryption loads before the operating system, there is no way of accessing the data without the password. This is an amazing feature that’ll help you meet data breach notification responsibilities defined by GDPR, HIPAA, and NESA. Moreover, it is a flexible and user-friendly software with a light impact on performance.
Another benefit of Jetico’s encryption software is that it is the only OS agnostic tool in the world for both Windows and Mac. It now encrypts hard drives with central management as well.
Key Features of Jetico’s BestCrypt Volume Encryption
- BestCrypt Volume Encryption leaves no room for your data to be lost. It encrypts the volume from where OS will load and the volume where OS stores the system files. If you encrypt the Boot volume or the OS System, authentication will necessarily be required before the OS loads. This pre boot authentication ensures that only you get access to your data.
- When it comes to algorithms, BestCrypt Volume Encryption uses strong algorithms for encryption, such as Twofish, Serpent, and AES. It’s two-layered security comes as an added advantage. The software also makes provision for an extra security layer, in the format of support for SafeNet eToken and Yubikey hardware tokens.
- Now no one can access your data even while you lose your pen drive! Jetico makes encrypted removable drives available. They are accessible on any computer using the user-password. What’s more? You don’t need to install the BestCrypt Volume Encryption on the computer you use the encrypted pen drive! Based on your requirements, you can either encrypt the entire computer, a single disk volume, or selected disc volumes.
- Peacefully leave your computer unattended if you use BestCrypt Volume Encryption. The software automatically locks it and requires authentication to wake up. The software allows automatic login to Windows by saving the encryption password. This will surely save time but is not recommended. What’s the purpose of having this encryption if you are autosaving the password? Isn’t it?
- For enhanced security against hackers, your encryption keys and passwords stay secure against interception. The software checks digital signatures of every module that boots the encrypted computer.
- Users can also configure Unattended Mount at Restart. This will securely store the encrypted keys within a Trusted Platform Module. The feature comes handy with servicing encrypted computers, remote management, or updating encrypted servers.
- And that is not all! Should an emergency scenario arise, Bootable USB, CD/DVD, Rescue File for Rescue decryption of non-system volumes, and Windows bootable Live CD are available at your disposal.
- Download and try the software completely free for 21 days.
System Requirements
Windows 10/8/7/Vista/XP, Server 2019/2016/2012/2011/2008/2003 (32 & 64 Bit Versions)
Mac OS x 10.9 & later
Summing up
Given the significance of data security of business-critical information for enterprises across domains, Jetico’s BestCrypt Volume Encryption comes out to be a wonderful hard disc encryption software for organizations. The new version 4 is even more user friendly and secure. Worthy enough to give it a try!
Don’t forget to share your experience with us. We would like to know your thoughts on the same!



